What is Maltego?
Maltego is proprietary software used for open-source intelligence and forensics, developed by Mean shift. Maltego focuses on offering a library of transforms for finding data from open sources and presenting it in a graph structure ideal for link analysis and data mining.
In addition to the fundamental entity types included in the software, Maltego allows you to create custom entities that can represent any data. The application’s primary goal is to analyze real-world links between people, groups, websites, domains, networks, internet infrastructure, and affiliations with social media sites like Twitter and Facebook.
Pros:
- Outstanding graph visualization software
- Data visualization possibilities are numerous.
Cons:
- It’s merely a Java program.
- The user interface has become obsolete.
Best 15 Maltego Alternatives
The alternatives to Maltego listed below were chosen by us or voted for by users. Tags and platforms can filter this list.
1. SpiderFoot
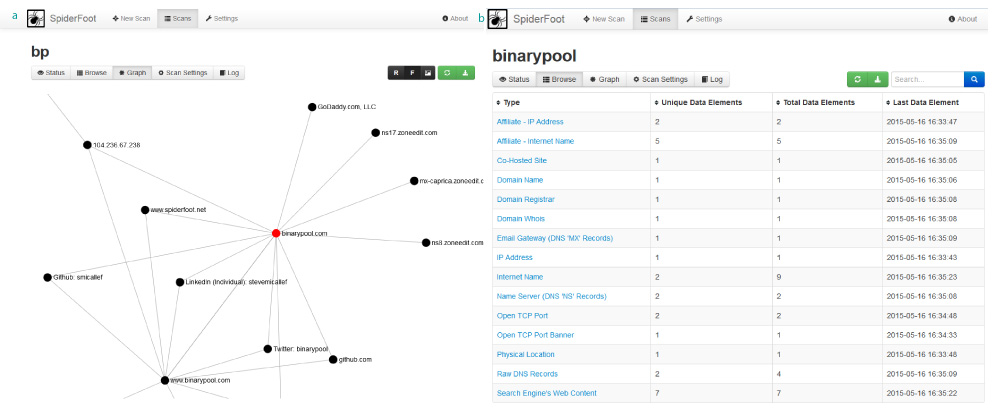
The technology aids in the automation of OSINT to uncover all possible outcomes for the target. It results in data integration with the available sources. It’s a type of reconnaissance tool that can assist in gathering intelligence on IP addresses, email addresses, and domain names and making it simple to specify the target that needs to be studied.
Features:
- Scanning is completed more quickly.
- Slack integration is available.
- Notifies users through email
- Importing scan targets assistance
- This results in timely investigations.
2. DataWalk
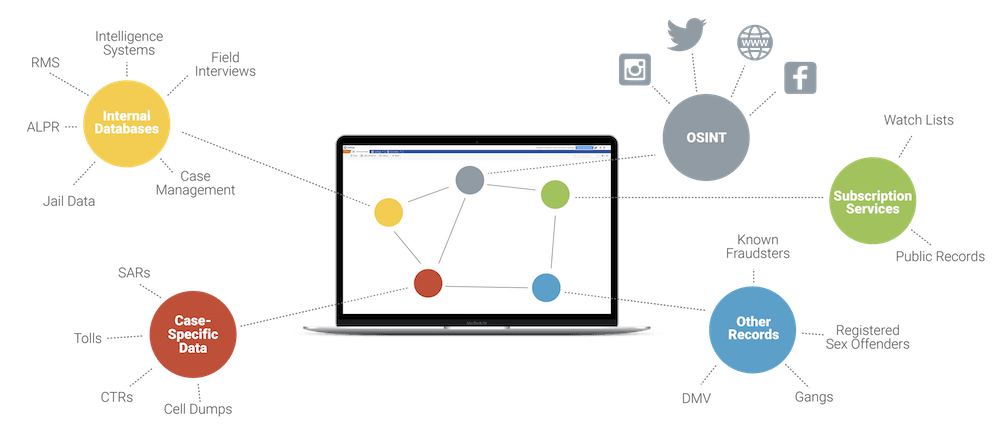
DataWalk is one of the most popular Maltego software alternatives. It’s the most advanced platform for uncovering patterns and connections. It also reveals inconsistencies in large-scale, multi-source intelligence operations. Things like link charts, histograms, timelines, and maps are disclosed in a single data view using options like intuitive visualization and the rest like link charts, histograms, timelines, and maps.
Features:
- All internal and external data are easily accessible.
- Triage and forensics are being sped up.
- Identification of suspicious claims in a timely and accurate manner.
- It’s simple to get influential risk scores.
3. Poortego
It is an open-source ruby project that assists with open-source intelligence linkage and storing. Poortego is a slow-moving but dynamic ecosystem with a substantial update recently. As part of the emerging community, it comprises neutral feelings. Poortego is bug-free and has no code smell.
Features:
- Windows, Mac, Linux, BSD, and Software are all supported.
- Has a unique and confidential database.
- Can make data mining and collection Essays easier to comprehend, with no requirement for technical training.
4. IBM i2 Analyst’s Notebook
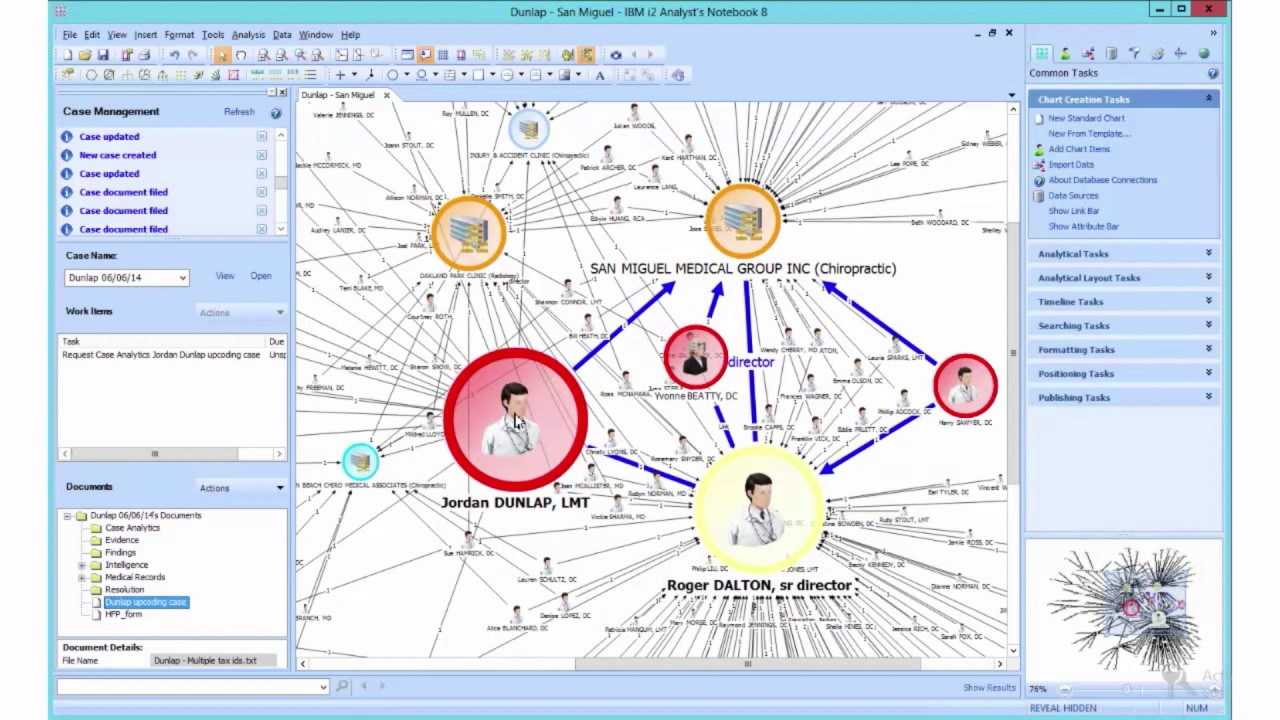
The family notebook can store and analyze data and visualize and disseminate information. It is the visual analytic tool that will assist in the transformation of data into intelligence. Innovative elements such as social network analysis and temporal and geospatial views will be included in the solution.
Features:
- Aids in the analysis of multidimensional visual data.
- Can quickly identify hidden connections
- Deals with the data pattern successfully.
- Criminals are identified and disrupted.
- Deals with phishing scams and cyber-threats
- Views that are temporal or geographical are included.
- Opinions that are temporal or geographical are included.
5. Sentinel Visualizer
It aids in empowering the constant needs of intelligence analysts and other areas such as law enforcement and the job of researchers and data workers. As part of the Big Data architecture, it is the next-generation data viewing and analyzing solution.
Features:
- As part of the primary data, it provides better insights into trends and patterns.
- The database-driven data visualization tool will enable fast visualization of multi-level connections between various entities.
- Is it the ideal model for various forms of relationships?
- Has special drawing and redrawing abilities.
- Creates optimal views that highlight the most important entities.
6. Gephi
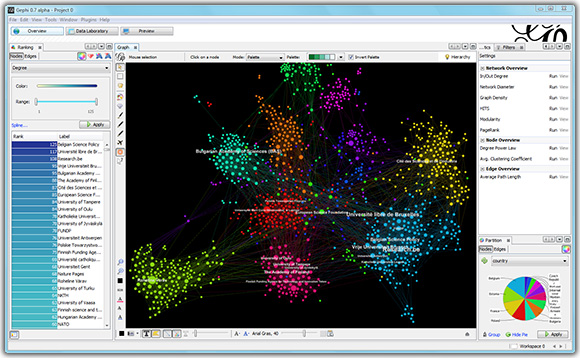
It’s the most recent open-source software for analyzing and visualizing data. It uses a 3D rendering engine to display real-time graphics and allow for quick exploration. It has a strong shear and tensile strength to it. The sound transmission is separated from the primary link here. Gephi is a soundproofing material that has been demonstrated to work.
Features:
- Rendering engine built-in
- File formats that are native and compatible
- Filtering in real-time
- Metrics and figures
- Importing and exporting data
- Algorithm for layout
7. snOint

The semi-automatic and the OSINT Framework with the exclusive package manager are now available. It protects IT and security experts more effectively. The alternative has a well-defined objective, and snOint makes things simple on the spot with its attacking function.
Features:
- Bug hunters will need this.
- Has the enumerating attack surface been discovered?
- The enumerating and attacking surface assists you in having a target concerning yourself.
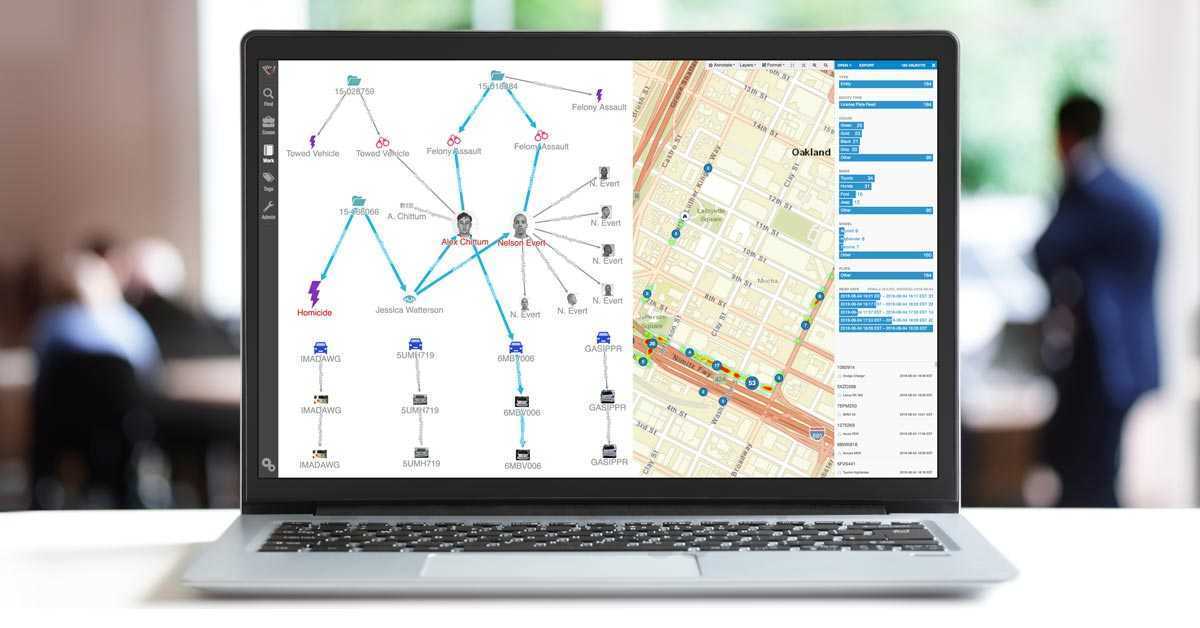
8. Linkurious
It enables on-site graphic visualization. It has an analysis platform that can assist in the detection of fraud. It is an alert system designed to help you detect dangers from all potential entities and real-time relationships. It is critical to have detection rules for identifying various suspicious attitudes.
Features:
- High-performance analytic and visualization software that can detect fraud and money laundering.
- It’s simple to set up and use and pretty flexible.
9. Visallo
It’s a different way to assist intelligence analysts. It can even help detectives and fraud investigators in law enforcement. It assists the analyst in gaining a better understanding by assisting in discovering intricate and hidden relationships in safeguarding enormous amounts of data on the fly. It will allow things to move more quickly and provide better awareness in a shorter period.
Features
- Access restrictions and permissions are made more accessible.
- Participates in collaborative tools.
- It has a dashboard that may be customized.
- Replication and migration of data are available.
- Has the ability to process large volumes of data
- Aids in the charting and management of incidents.
10. Lampyre
It’s an OSINT multi-tool designed to help you analyze data effectively. It allows for data analysis and visualization in one place. In terms of business, it provides a quick data analysis tool. It will also enable users to perform at their best in data analysis and visualization. At the same time, it aids in the management of company data and processed data for improved analysis.
Features:
- It is a powerful data selector.
- It includes points as well as last names.
- Assists in the creation of data and source interconnections.
- In one simple click, data is enhanced.
11. Siren.io

It’s the ideal solution for extensive data search and analysis, knowledge graphs, connection analysis, and the most comprehensive stream monitoring and warning system. In the realm of investigative intelligence, Siren is a well-known platform. It can aid in the resolution of challenging industry issues, and in this scenario, traditional BI is beneficial.
Features:
- Link-based integrated analysis
- The navigation of the investigative dashboard
- As part of the graph, immense data aggregations
- In the case of link analysis, the feature of beating the congestion and the challenge.
- The nodes that form a group
- The investigation of dynamic data
- The use of graph lenses to achieve a better focus
- As part of the industry, the extensive and powerful expanding control
12. Shodan
Shodan is a searchable database of digital intelligence. It’s a search engine for locating information on IP addresses, ports, and other Internet-connected devices. It can, for example, be used to collect data from servers belonging to businesses or even cities.
Features:
- Service accessible via the internet
- This is a free edition.
- A query language that is unique to the company
Type in any business to acquire information on the devices used by the company, including honeypot ICS, location, services (HTTP, etc.), and even any vulnerabilities the devices may have.
Network names or IP addresses organize the information. What OS systems are being utilized, what open ports are being used, what type of Internet service is being used, what website design language is being used, and much more are all part of the host information. It’s also feasible to scan a network for bulk data using Classless Inter-Domain Routing (CIDR) or an IP range.
13. Metasploit

This program isn’t timid; on the contrary, it’s a fearless weapon that can gather all of the necessary data on a target – whether it is a host or a network – and then exploit any vulnerabilities that have been uncovered. This is usually accomplished by sending a payload that contains commands to be executed.
Features:
- A free version of a penetration testing tool
- Hacking systems are included.
Users can use Metasploit to upload, download, listen to, or change files they’ve found. They can even take screenshots and activate the camera and microphone for remote eavesdropping on mobile devices.
14. Recon-ng
Another valuable tool for obtaining information from open public records is this one. Although the CLI makes the interface appear intimidating at first, it is a simple tool to understand after a few days of playing around with it.
Anyone who is experienced with working in a Unix/Linux environment, on the other hand, will find this to be a familiar tool.
Features:
- Linux command-line utility
- It is entirely free to use
- Plug-ins created by the community
There are default modules in Recon-ng that are also open source, and there is also a marketplace where you may add even more capabilities. It also continues to change and grow as the developer community contributes because it is an open-source tool. Recon-ng is a web-based open-source reconnaissance application written in Python. As a result, it cannot be exploited in exploits.
15. SpiderFoot

We have a utility that can be downloaded and installed on a Linux or Windows machine and a cloud version that can be run from a browser with SpiderFoot.
Features:
- It’s cloud-based and may be viewed via a browser.
- For Windows and Linux, there is an on-premises alternative.
- Identifies security flaws
- Detects accounts that have been compromised.
The free online version, SpiderFoot HX, provides five scans every month. Once the target (or a group of marks in the form of domain names, user names, IP addresses, and so on) has been chosen, the tool launches a large scan that automatically begins digging for troves of data from over 100 public data sources.
Conclusion :
If you’re a data investigator or analyst, we understand how difficult it is to analyze and change data. Data visualization and analysis might be complex, but the internet has simplified the process.
You may discover many tools to help you with data analysis on the internet, but most of it is spam, and only a few of them work.
As previously said, Maltego is one of the most reputable platforms for data-related services such as data gathering and analysis.
It’s a fantastic open-source data analysis program with dynamic data interpretation and threat detection capabilities. However, because the platform’s subscription fees are a little high, most investigators and data analysts avoid using it.




















